Cat’s Got Your Files: Lynx Ransomware
Key Takeaways
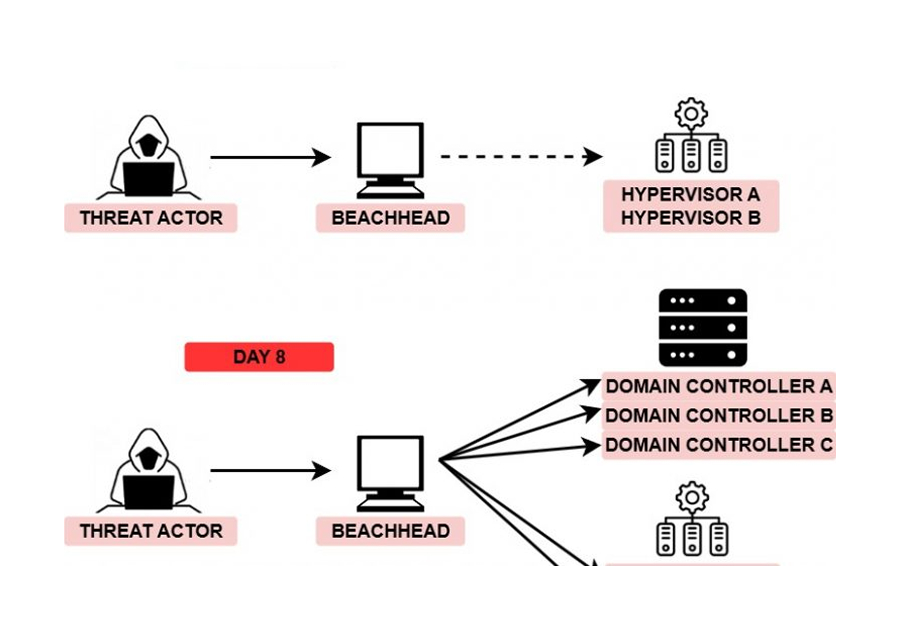
- The intrusion began with a successful RDP login using already-compromised credentials, likely obtained via an infostealer, data breach reuse, or an initial access broker.
- Within minutes, the threat actor moved laterally to a domain controller using a separate compromised domain admin account, created multiple impersonation-style accounts, and...
The Lynx ransomware attack serves as an example of the sophisticated tactics cybercriminals employ, including remote access, data encryption, and system manipulation. The attackers use a variety of techniques to exploit vulnerabilities in systems and maintain their presence, making it challenging for defenders to respond effectively. It is crucial to understand these patterns and develop strategies that address the root causes of such attacks, rather than merely reacting to individual incidents....