From Bing Search to Ransomware: Bumblebee and AdaptixC2 Deliver Akira
Overview
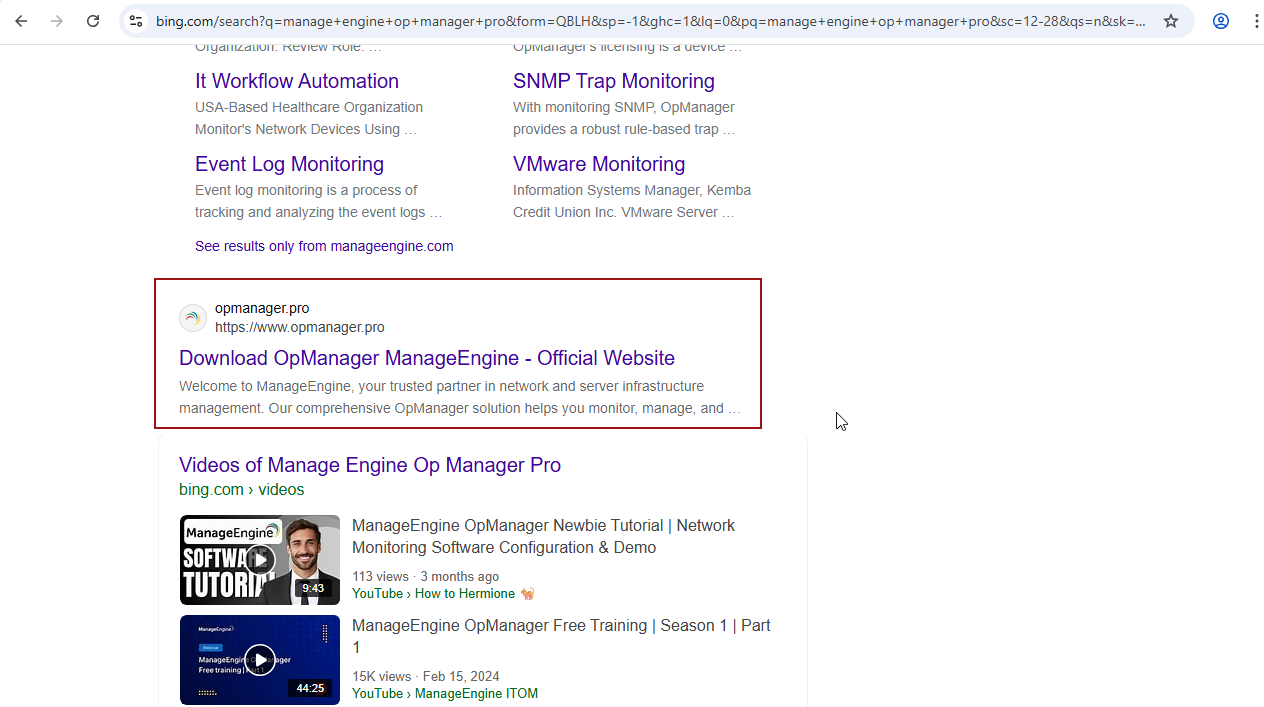
Bumblebee malware has been an initial access tool used by threat actors since late 2021. In 2023 the malware was first reported as using SEO poisoning as a delivery mechanism. Recently in May of 2025 Cyjax reported on a campaign using this method again, impersonating various IT tools. We observed a similar campaign in J...
The Dark Halo campaign serves as a reminder of the ever-present risk of sophisticated cyberattacks targeting critical infrastructure. By exploiting vulnerabilities in MSP software, the attackers were able to gain access to the networks of multiple organizations simultaneously. The use of custom malware and stealthy tactics underscores the sophistication and determination of the threat actor.
The response to this incident highlights the importance of collaboration between cybersecurity firms to s...